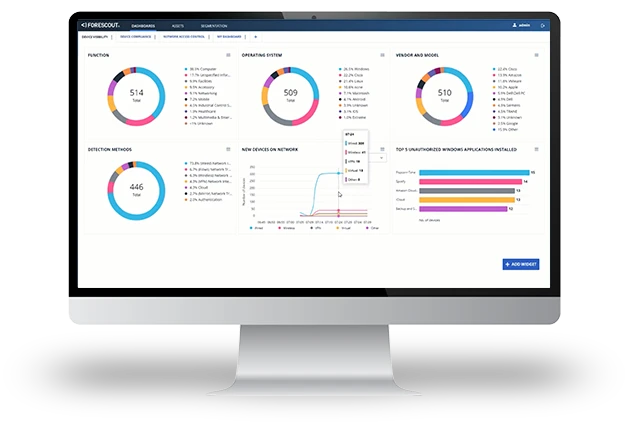
UZTNA
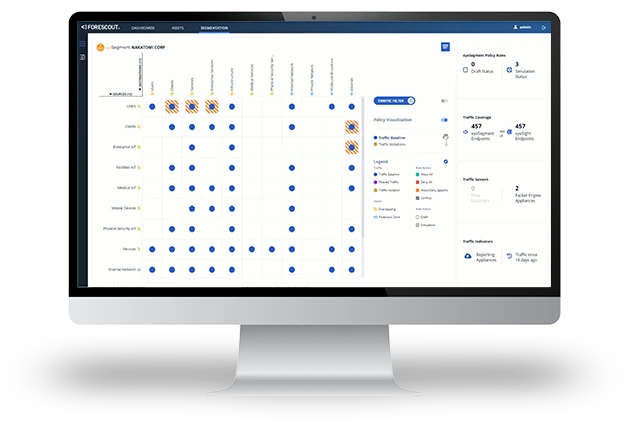
Forescout delivers adaptive Universal Zero Trust Network Access for IT, IoT, IoMT, and OT — on-premises and remote.
Secure access without compromise. Forescout’s UZTNA delivers a unified, adaptive framework that applies Zero Trust principles to every connection, every device, and every user — without slowing down your business.