OT Security
Reduce operational and Cyber-Physical Systems risk in OT/ICS and SCADA environments
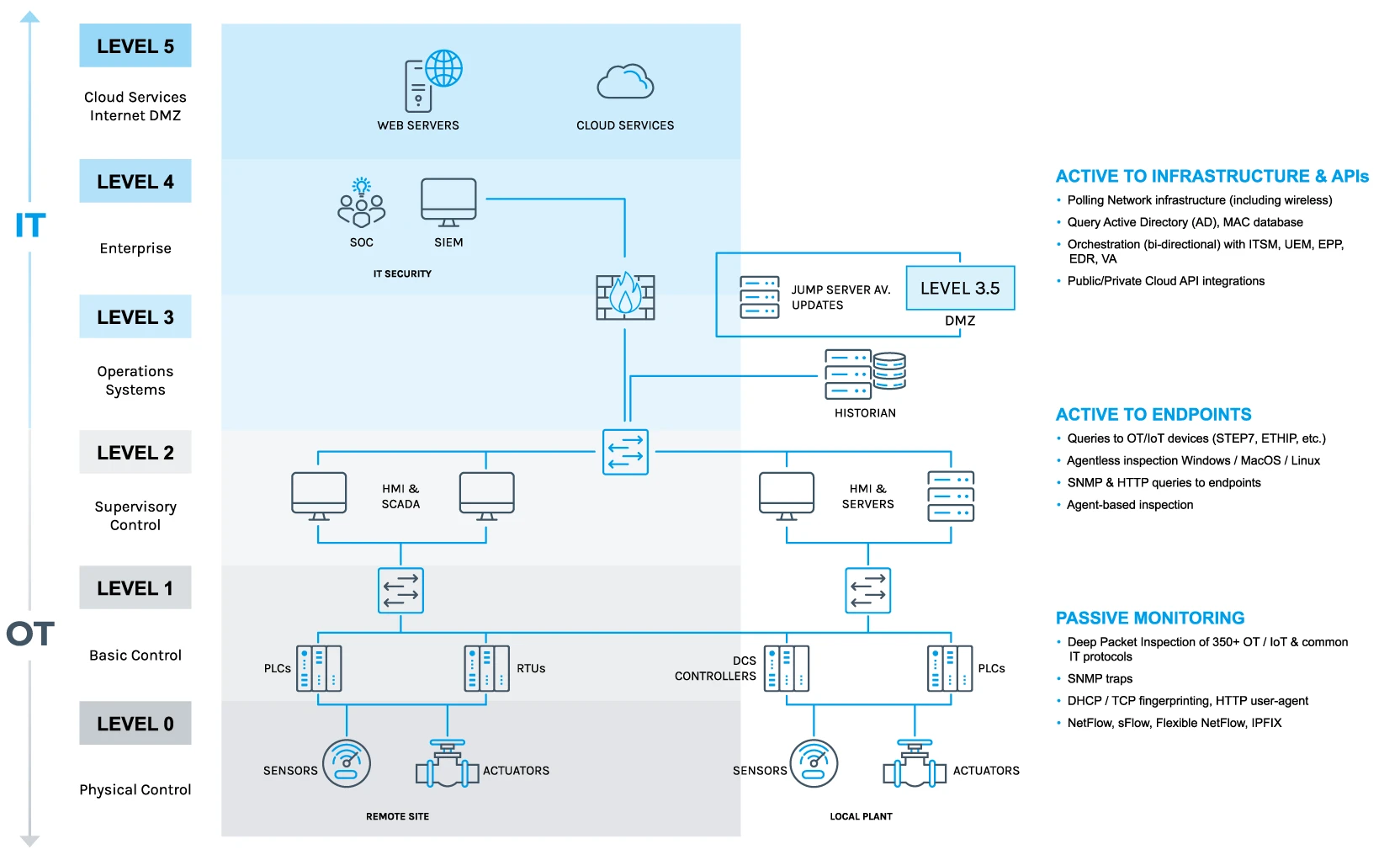
Industrial digitalization has accelerated the convergence of IT, IoT and OT assets and networks, increasing the complexity and vulnerability of previously isolated OT and ICS networks.
With industrial environments increasingly dependent on Cyber-Physical Systems (CPS) for production, you need a protection platform with continuous asset discovery, assessment, and governance to ensure regulatory compliance and avoid downtime – so you can detect and remediate cyber threats before they lead to operational incidents.
One Platform.
Built to Protect What Can’t Fail.
Complete coverage nobody else delivers.
Other OT security solutions stop at visibility and detection. We go further. We don’t just show you what’s wrong. We help you act — contain threats, enforce policy, and continuously improve your security posture across IT, OT, IoT, IoMT, and CPS environments.
Defining clear security zones and enforcing policy-based segmentation is a first line of defence in industrial networks. The Forescout 4D™ Platform establishes this foundation to control access, reduce exposure, and enable a practical path to universal ZTNA in industrial environments.


Real Orchestration Beyond Integration
You choose the best technology, we make it work together.
We unify tools into a single, coherent view with shared context, consistent data, and metrics across your stack. More than surface-level integration, this is unified orchestration that delivers smarter workflows, faster decisions, and better use of what you already use.





Deploy What You Need, How You Need It
Deploy on your terms — without redesigning your architecture.
Cloud, on-prem, air-gapped, or hybrid, we adapt to your environment. From passive monitoring to active queries, agent-based or API-driven. Deploy with our proprietary appliances, build your own sensors, or run directly our containers on existing networking equipment.
Threat Intelligence That Speaks OT
See what’s coming, because we’ve already seen it.
Backed by over a decade of focused ICS research, our threat intelligence transforms raw signals into actionable insight. From ransomware to supply chain attacks and living-off-the-land techniques, we deliver context that helps you understand what’s relevant, prioritize what’s dangerous, and act before threats impact your operations.
The OT Security Platform Industrial Leaders Trust
Proven in the world’s most complex industrial environments.
Global manufacturers, energy providers, MoDs, and critical infrastructure operators rely on our platform to keep operations safe, resilient and compliant. See how our customers replaced fragmented tools with a scalable platform that aligns security with business goals.

![]()


Related Products
eyeInspect
Gain complete device visibility through deep packet inspection of all industrial network protocols and baseline assets.
explore