Cyber Asset Inventory
Gain complete asset visibility across your attack surface
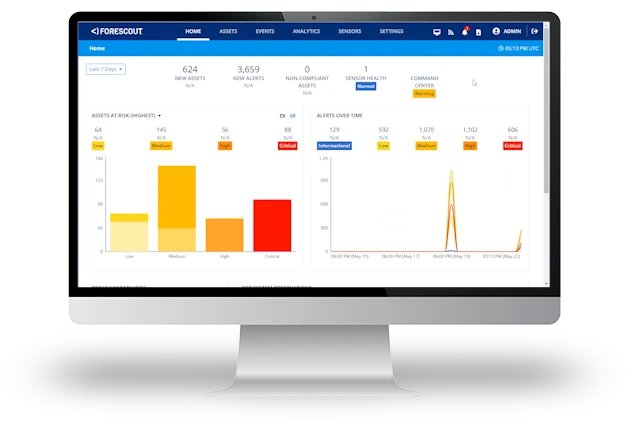
Attack surface growth is outpacing your security team’s ability to identify, quantify and prioritize risk and exposure. The first step is maintaining an accurate, real-time asset inventory with in-depth device context for all IP-connected assets in one normalized view.
Eliminate error-prone manual processes with continuous, automated discovery, classification and assessment of every device, managed and unmanaged.
100% Asset Visibility with Forescout
As a baseline, this energy company only had visibility into its 50,000 agentable assets. Fragmented information from 32 separate security tools identified closer to 200,000 connected devices.
In just one week, without relying on any software agents, Forescout identified more than 235,000 total assets – revealing an 80% security risk gap over agent solutions and creating a single source of truth.
Asset Inventory and Visibility Challenges
Why Forescout for Cyber Asset Inventory

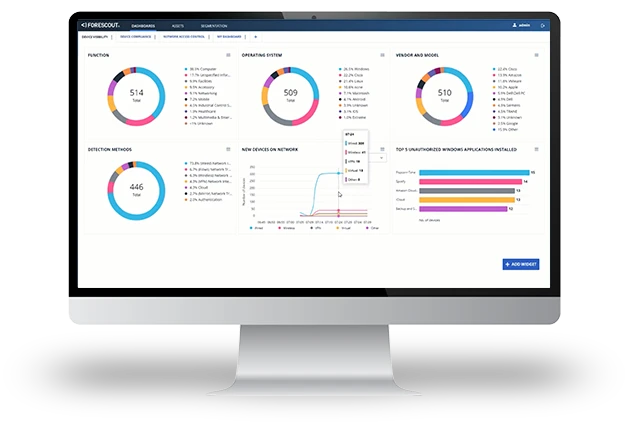
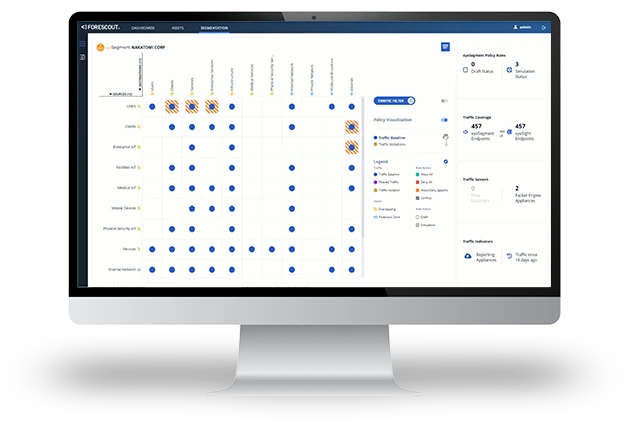
Real-Time Asset Intelligence for Better Security and Business Decisions
Many standards, frameworks and regulations require organizations to maintain an accurate asset inventory. To support informed security decisions, you also need rich context about each device. The Forescout 4D Platform™ collects data on device type, manufacturer, OS configuration, applications installed, patch state, network location, logged-in users, vulnerabilities, criticality and what it’s communicating with.
All of this can be continuously synchronized with your configuration management database (CMDB), such as ServiceNow, to prove a wealth of contextual information as assets join and leave the network and accelerate incident response.
Forescout Device Cloud
18.7M
Unique device profiles
6500+
Vendors
2200+
OS versions
Flexible. Versatile. Rapid Deployment.
Forescout offers unmatched deployment flexibility to meet the diverse hardware and cloud requirements of modern environments. We ensure compatibility with existing infrastructures while minimizing operational disruption. This versatility makes it an ideal choice for your organization. If you seek robust, scalable solutions tailored to your unique operational and regulatory landscapes, look no further.
The Forescout 4D Platform™ adapts seamlessly with options for on-premises installations, virtual machines and Docker-based containerized deployments, including:
- Air-gapped systems for high-security needs
- Forescout appliances that deliver maximum visibility and control
- Hybrid configurations to connect distributed sites
- Fully cloud-based operations for scalability
…and Sensors that can be deployed as:
- Standalone appliances
- Installed directly on routers and switches for quick implementation without production disruption
- Or configured as active sensors to query network infrastructure
Deploy Forescout on Phoenix Contact Security Solutions Industrial Switching Platform for enhanced security and simplified deployments

Reduce physical hardware and deploy Forescout in Azure – a scalable, robust and cost-effective solution
Deploy Forescout on Keysight packet brokers for efficient and scalable deployments
Leverage the Dell Validated Design for Energy Edge to deploy in substations with ABB and Forescout
Related Products
1The State of IoT and OT Cybersecurity in the Enterprise, Ponemon Institute, 2021
2Cybersecurity Asset Management Trends 2021, Enterprise Strategy Group