Flexible. Versatile. Rapid Deployment.
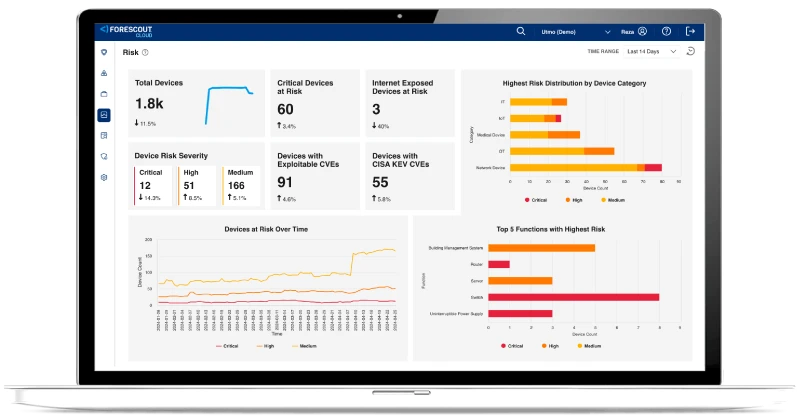
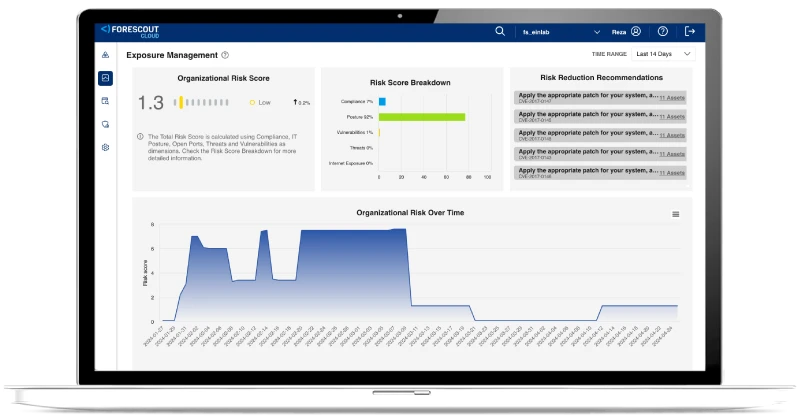
Forescout offers unmatched deployment flexibility to meet the diverse hardware and cloud requirements of modern environments. We ensure compatibility with existing infrastructures while minimizing operational disruption. This versatility makes it an ideal choice for your organization. If you seek robust, scalable solutions tailored to your unique operational and regulatory landscapes, look no further.
The Forescout 4D Platform™ adapts seamlessly with options for on-premises installations, virtual machines and Docker-based containerized deployments, including:
- Air-gapped systems for high-security needs
- Forescout appliances that deliver maximum visibility and control
- Hybrid configurations to connect distributed sites
- Fully cloud-based operations for scalability
…and Sensors that can be deployed as:
- Standalone appliances
- Installed directly on routers and switches for quick implementation without production disruption
- Or configured as active sensors to query network infrastructure
Deploy Forescout on Phoenix Contact Security Solutions Industrial Switching Platform for enhanced security and simplified deployments

Reduce physical hardware and deploy Forescout in Azure – a scalable, robust and cost-effective solution
Deploy Forescout on Keysight packet brokers for efficient and scalable deployments
Leverage the Dell Validated Design for Energy Edge to deploy in substations with ABB and Forescout