UZTNA
Forescout delivers adaptive Universal Zero Trust Network Access for IT, IoT, IoMT, and OT — on-premises and remote.
Secure access without compromise. Forescout’s UZTNA delivers a unified, adaptive framework that applies Zero Trust principles to every connection, every device, and every user — without slowing down your business.
Why UZTNA Matters
Modern enterprises face unprecedented complexity. Devices are everywhere – laptops, servers, medical equipment, industrial controllers – connecting from offices, homes, and cloud environments. Traditional Zero Trust approaches often stop at managed IT endpoints, leaving blind spots that attackers exploit. Fragmented visibility and inconsistent policies create security gaps, complicated compliance, and slow response.
The result? Increased risk, operational inefficiency, and exposure to insider threats.
The Forescout 4D Platform™
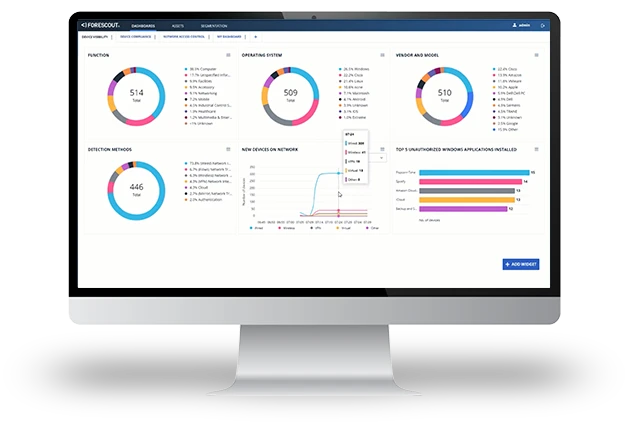
Comprehensive Visibility
Real-time discovery and classification of all devices—managed or unmanaged
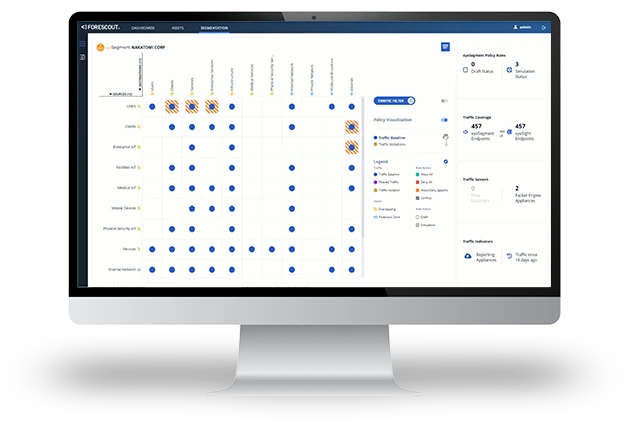
Dynamic Policy Enforcement
Enforce least-privilege access and segmentation policies driven by device identity, risk attributes, and continuous East-West traffic visibility — not just IP addresses
Continuous Compliance
Automated evidence collection and policy validation for frameworks like CIS and NIST
Adaptive Threat Defense
Behavioral analytics and anomaly detection to prevent insider risk and data loss
Business Outcomes
UZTNA: The Next Evolution in Secure Network Access
Modern enterprises operate across diverse environments: IoT, IoMT, OT, and CPS – requiring a unified security model that extends beyond traditional Zero Trust. UZTNA delivers this by consolidating access control, identity verification, and continuous East-West traffic monitoring into a single, adaptive framework. Network segmentation is a core pillar of this framework, with policies shaped by device identity and risk posture rather than IP addresses alone. Every session is dynamically validated to ensure trust is never assumed.
How Forescout Powers a UZTNA Architecture
In a UZTNA model, security decisions are not limited to isolated network segments — they span users, devices, and applications across hybrid environments. A centralized Policy Decision Point (PDP) continuously evaluates identity, device posture, and contextual risk signals to determine the appropriate access level. These decisions are then enforced dynamically across multiple Policy Enforcement Points (PEPs), ensuring consistent, least-privilege access everywhere. Forescout enables this unified approach by integrating visibility, risk-based access control, and orchestration across diverse vendors and technologies, delivering a seamless, adaptive UZTNA experience.
Your journey to Universal Zero Trust Network Access starts with the Forescout 4D platform™: the only platform for UZTNA powered by agentic AI.
Device Visibility & Classification
Network-based discovery produces a list of IP addresses – many vendors stop here. The Forescout 4D Platform™ combines intelligence sources to classify and group raw IP addresses into your business taxonomy.
Traffic Analysis & Visualization
An intuitive, attribute-driven matrix of traffic among all connected assets enables segmentation compliance and policy design based on device identity, risk context, and observed communication patterns.
Policy Impact Simulation
Simulate segmentation designs using actual traffic flows and risk overlays to validate controls, fine-tune policies, and flag violations before enforcement, without causing costly business disruptions.
Central Policy Decision Point
The Forescout 4D Platform™ analyzes 800+ data points from activity logs, threat intelligence, compliance, identity management, SIEMs and more to orchestrate policy enforcement among your PEPs.
Reach Zero Trust Mandates with an Adaptive Approach
As organizations work to meet regulatory requirements, adopting Zero Trust Architectures can feel overwhelming, especially when managing expansive networks with millions of connected devices. The rise of unmanaged OT/IoT devices further complicates security, increasing the risk of audit failures and breaches. Discover how an adaptive approach to Zero Trust with UZTNA can streamline the process and help organizations achieve compliance more efficiently.
Flexible. Versatile. Rapid Deployment.
Forescout offers unmatched deployment flexibility to meet the diverse hardware and cloud requirements of modern environments. We ensure compatibility with existing infrastructures while minimizing operational disruption. This versatility makes it an ideal choice for your organization. If you seek robust, scalable solutions tailored to your unique operational and regulatory landscapes, look no further.
The Forescout 4D Platform™ adapts seamlessly with options for on-premises installations, virtual machines and Docker-based containerized deployments, including:
- Air-gapped systems for high-security needs
- Forescout appliances that deliver maximum visibility and control
- Hybrid configurations to connect distributed sites
- Fully cloud-based operations for scalability
…and Sensors that can be deployed as:
- Standalone appliances
- Installed directly on routers and switches for quick implementation without production disruption
- Or configured as active sensors to query network infrastructure
Deploy Forescout on Phoenix Contact Security Solutions Industrial Switching Platform for enhanced security and simplified deployments

Reduce physical hardware and deploy Forescout in Azure – a scalable, robust and cost-effective solution
Deploy Forescout on Keysight packet brokers for efficient and scalable deployments
Leverage the Dell Validated Design for Energy Edge to deploy in substations with ABB and Forescout
Related Products
1 2024 Gartner Emerging Tech: Universal ZTNA Drives Secure Access Consolidation report
2 Zero Trust Adoption Report 2021, Microsoft
3 Gartner Identifies Three Factors Influencing Growth in Security Spending, Oct. 13, 2022