Securely Maintaining Business Continuity with eyeSegment
Securing Today’s Remote Workforce
In these challenging times we’re living in, it seems like everyone is now working from home—and that has consequences. As the remote connectivity landscape transitions to a new paradigm, organizations are trying to maximize cybersecurity and minimize the potential for costly business disruptions that could diminish organizational confidence, stall progress and negatively impact the bottom line.
Managing the inherent risks associated with the expansion of remote access connectivity during a time of crisis has become top-of-mind for IT teams. The sudden nature of the remote workforce expansion, coupled with supply chain challenges, has required organizations to relax restrictions on remote users connecting via personal devices. The hygiene of these devices is less likely to be maintained against known-compliant images, and they are more likely to go unpatched, unprotected and unmonitored. Simply installing VPN clients on these devices is insufficient and represents a threat vector. And, as you’d expect, reduced or incomplete visibility of remote users’ devices and behavior, along with insufficient network controls on home networks, makes it very difficult for IT teams to connect their remote workforce while protecting their organizations’ sensitive data and processes.
Aside from dealing with device posture state and hygiene concerns, changing communication patterns on the network must be understood and addressed. As shown in the figure below, different types of remote users communicate with different types of resources or internal devices so they can continue to get work done. Using traditional approaches and having to analyze multiple traffic logs can make it really hard to understand remote user communications patterns—all of which increase operational costs and complexity while taxing limited resources and skillsets.
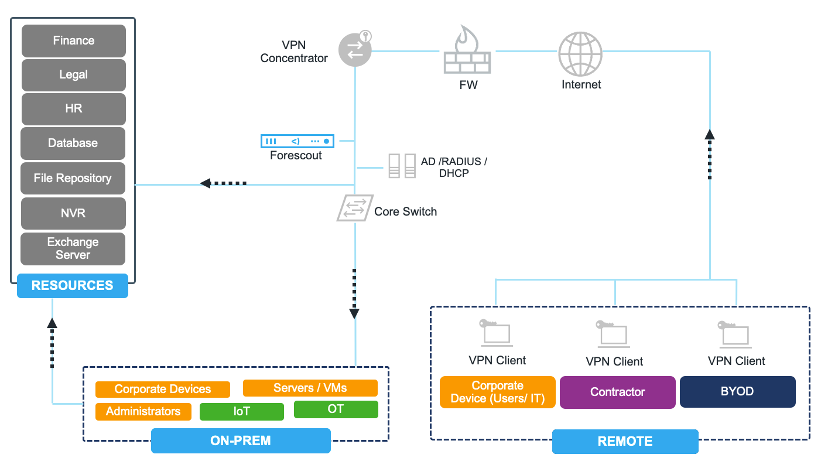
Figure 1: Different remote users accessing resources and on-premise devices
To be able to effectively adapt to the new remote workforce paradigm, organizations need a simple and automated approach to network segmentation. Continuous traffic monitoring and effective policy enforcement are essential to prevent cyber incidents while users are connected remotely through VPNs. Best practices, such as Zero Trust security and least-privilege access, must be enforced.
The Forescout platform, including Forescout eyeSegment, bridges disparate enforcement technologies to keep misbehaving or compromised devices from introducing risk across the extended enterprise. The platform helps to maintain device compliance posture and limit the attack surface by providing complete visibility of all connected endpoints and their communication patterns regardless of where and how they connect to the network. Forescout offers the platform, tools and expertise to help our customers:
Visualize remote user and device communications in real time
- Visualize traffic patterns and understand your remote user behavior in minutes without making any changes to your infrastructure, and still leverage your existing enforcement technologies.
Design, simulate and monitor segmentation policies
- This baseline traffic visibility is foundational for defining authorized vs. unauthorized traffic communications, helping you design your security and segmentation policies based on your business logic. The platform lets you simulate these policies before enforcing them, so there’s no impact on business continuity.
Reduce risk and maintain compliance
- Overall, this approach helps you reduce risk in your environment and maintain device compliance posture through a new lens: network traffic.
There are many different scenarios that require variations of access rules based on different types of users or connected devices. A few examples include:
- A remote user needs to access resources through their on-prem corporate PC because there are legacy applications that can only be accessed locally in the network
- The organization allows employees to use their BYOD devices
- A contractor needs access to some resources but is not allowed to access on-prem devices
- Corporate users require different levels of access to resources or other parts of the organization, depending on their business needs and the organization’s access policies.
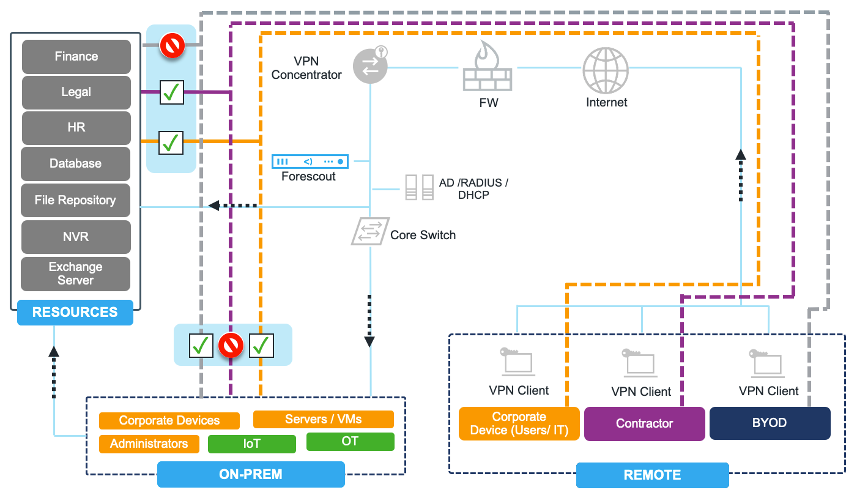
Figure 2: Remote user communication pattern examples
So, as you understand and visualize authorized/unauthorized flows, you can design granular and logical segmentation policies based on your business needs and compliance requirements, and can easily simulate the policies before going operational. When you decide to enforce your policies, you can continuously monitor and act on policy violations to ensure segmentation hygiene.
Forescout eyeSegment assists IT and security teams in maintaining network segmentation hygiene by helping you:
- Visualize remote user VPN traffic flows and identify violations
Continuously monitor remote traffic
Through the eyeSegment Matrix, you can quickly visualize remote user traffic patterns across your extended environment that are coming through a VPN and going to various destinations. The other way to visualize VPN traffic is to drill down to All Users Zones in the eyeSegment Matrix. This allows you to visualize VPN communications between logical business groups in real time and identify traffic violations based on policies.
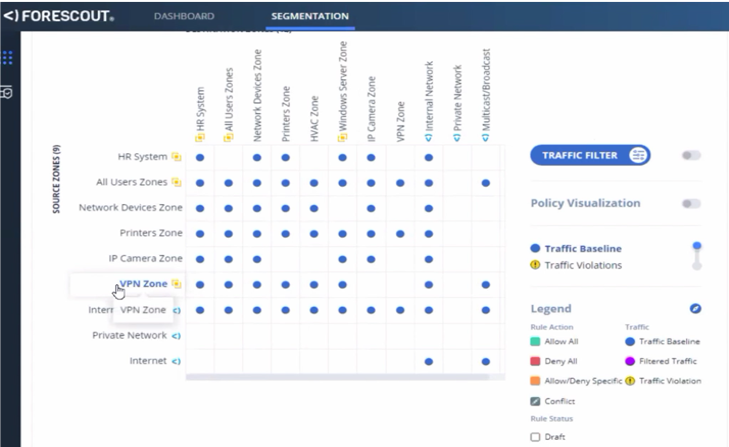
Figure 3: Real-time view of VPN communications in eyeSegment Matrix
- Act on identified traffic violations
Ensure authorized VPN access based on assigned business roles
Anticipating eyeSegment policy violations, policies can be configured to generate violation notifications automatically so you can take required actions such as email notifications, syslog alerts and ServiceNow ticket creation. When you want to dynamically terminate noncompliant VPN connections or stop unauthorized traffic flows, Forescout eyeControl and eyeExtend can orchestrate eyeSegment policies and automate controls across heterogeneous enforcement technologies. eyeControl enables consistent enforcement of context-aware segmentation policies and controls with existing security and infrastructure technologies—eliminating the need for agents. eyeExtend modules orchestrate controls via out-of-the-box integrations with leading next-generation firewalls (NGFWs).
WATCH WEBINAR
Watch Webinar – Move Beyond VPN to Secure Your Remote Workforce
Learn More