The Forescout 4D Platform™
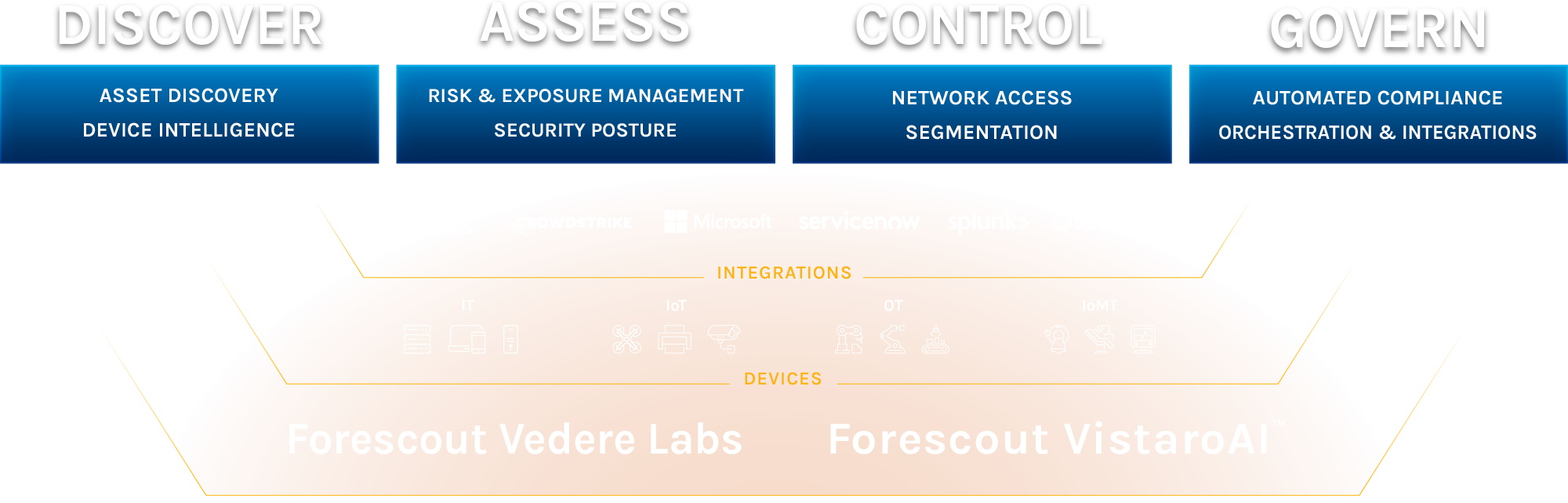
Discover. Assess. Control. Govern.
Your journey to Universal Zero Trust Network Access starts with the Forescout 4D platform™: the only platform for UZTNA powered by agentic AI. Continuously identify, protect, and ensure the compliance of all assets – IT, IoT, IoMT and OT – regardless of location, automatically. Deliver cloud-native network security intelligence boosted by agentic workflows from the pioneer of traditional NAC.
Shift from reactive firefighting to proactive risk management. Get continuous visibility into what’s actually exposed across every connected asset — managed or not, physical or virtual. The result? Priorities managed. Peace of mind.
What the Forescout 4D Platform™ Can Do for You
Get visibility, take control, and automate compliance as part of your Zero Trust implementation with Forescout